Navigating the digital realm offers a unique challenge: maintaining ownership over your personal information. Every click, every post, and even inactivity leaves a trace. This digital footprint can be vast, encompassing everything from social media profiles. While the internet offers incredible opportunities for connection and growth, it's crucial to appreciate the implications of this enduring record. Thankfully, you aren't powerless against your digital past. Utilizing a range of strategies, how to remove online personal information you can actively reduce your online presence and reclaim your privacy.
- Start by pinpointing all your online accounts.
- Scrutinize the information associated with each account and consider what can be altered.
- Research privacy settings and adjust them to restrict data sharing.
Yelp Removal 101: How to Take Control of Your Business Listing
Want the most up-to-date listing for your enterprise displayed on Yelp? Taking control of your business profile is the first step. managing inaccurate reviews or simply want to improve your online presence, removing negative content can be crucial.
Yelp offers a straightforward process for managing your listing, including the ability to flag inappropriate reviews and submit a takedown request unwanted information.
- Understanding Yelp's policies is key. Familiarize yourself with their guidelines on what constitutes acceptable content and review practices.
- Be polite but firm in your communication with Yelp reviewers and representatives.
- Document any issues thoroughly, including screenshots and relevant details.
By monitoring and addressing your Yelp listing, you can ensure accuracy. Remember, taking control of your online image is essential for business success in today's digital world.
Vanishing Act : Securing an Anonymous Phone Number for Online Use
In the sprawling online realm, protecting your identity is paramount. While email addresses can be easily hidden, phone numbers often remain a glaring vulnerability. Hackers can exploit your number for harassment, malicious purposes. That's where anonymous phone numbers come into play, offering a layer of privacy that shields your real contact information from prying eyes.
There are various methods for obtaining an anonymous phone number. One popular choice is to utilize a dedicated service that provides virtual phone numbers, allowing you to make and receive calls without revealing your true identity. These services often possess advanced privacy settings to further protect your data. Another route is to acquire a burner phone – a prepaid device specifically designed for temporary use. While this method offers less flexibility than virtual numbers, it provides a tangible separation between your online and offline lives.
- Consider the level of anonymity you require. Are you simply looking to shield your number from spam calls, or do you need a higher degree of privacy for sensitive transactions?
- Research different service providers and compare their features, pricing, and credibility. Read user reviews and engage with online forums to gain insights into the experiences of others.
- Once you've chosen a provider, carefully review their privacy policy to understand their data policies. Ensure that they align with your expectations for anonymity.
Securing Your Online Presence: Mastering Internet Privacy
Navigating the digital landscape requires vigilance regarding your online privacy. Every click, search, and interaction leaves a trace of your activity. While the internet offers incredible opportunities for collaboration, it also presents risks to your privacy. Thankfully, there are effective strategies to control your digital footprint and safeguard your sensitive information.
- Start by understanding the types of data you share online. This includes everything from your browsing history to digital interactions and even transactions.
- Implement strong passwords for all your services. Consider a password generator to securely store and create complex passwords.
- Audit your privacy configurations on social media platforms and other websites. Control the information you share publicly and be mindful of permissions granted to apps.
Continuously monitor your credit reports for any signs of fraud. Employ security software, such as antivirus and anti-malware programs, to defend your devices from online attacks.
Your virtual trail is more vulnerable than you think. Every update can be weaponized by someone with malicious intentions. Before it's too late, take control of your data and minimize the risk of becoming a victim.
It's crucial to frequently audit your social media accounts. Delete anything that could be leaked for harm. Be mindful of the private facts you display online.
Remember, it's better to be highly protective than fall prey.
Reclaim Your Digital Footprint: A Step-by-Step Guide to Internet Privacy
Navigating the digital landscape presents a minefield of privacy concerns. From data-hungry corporations to opportunistic actors, your personal information is constantly at risk. But don't fret!|However|Fear not! You possess the power to take back your online identity and safeguard your digital footprint. This comprehensive guide will equip you with the strategies to navigate the digital world securely.
- Start with a review your current online presence. Identify the platforms where you share information and assess their privacy settings.
- Then, bolster your passwords. Utilize complex passwords for each account and consider using a dedicated tool to retain them.
- Limit the data profile. Only provide required information online and be cautious about external applications that seek access to your personal data.
By following, you can greatly improve your online privacy and protect your identity in the digital realm.
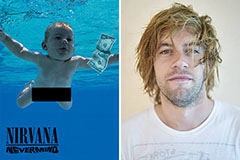 Spencer Elden Then & Now!
Spencer Elden Then & Now! Kelly McGillis Then & Now!
Kelly McGillis Then & Now! Hailie Jade Scott Mathers Then & Now!
Hailie Jade Scott Mathers Then & Now! Lacey Chabert Then & Now!
Lacey Chabert Then & Now! Morgan Fairchild Then & Now!
Morgan Fairchild Then & Now!